
The following article on Cheating in Online Poker emphasizes the lesson of "... Never enter the territory of the opposition without a superior advantage. "
###
From http://www.schneier.com/blog/
Cheating in Online Poker
http://freakonomics.blogs.nytimes.com/2007/10/17/the-absolute-poker-cheating-scandal-blown-wide-open/
Fascinating story of insider cheating: Some opponents became suspicious of how a certain player was playing. He seemed to know what the opponents' hole cards were. The suspicious players provided examples of these hands, which were so outrageous that virtually all serious poker players were convinced that cheating had occurred. One of the players who'd been cheated requested that Absolute Poker provide hand histories from the tournament (which is standard practice for online sites). In this case, Absolute Poker "accidentally" did not send the usual hand histories, but instead sent a file that contained all sorts of private information that the poker site would never release. The file contained every player's hole cards, observations of the tables, and even the IP addresses of every person playing. (I put "accidentally" in quotes because the mistake seems like too great a coincidence when you learn what followed.) I suspect that someone at Absolute knew about the cheating and how it happened, and was acting as a whistle- blower by sending these data. If that is the case, I hope whomever "accidentally" sent the file gets their proper hero's welcome in the end.
Then the poker players went to work analyzing the data -- not the hand histories themselves, but other, more subtle information contained in the file. What these players-turned-detectives noticed was that, starting with the third hand of the tournament, there was an
observer who watched every subsequent hand played by the cheater. (For those of you who don't know much about online poker, anyone who wants can observe a particular table, although, of course, the observers can't see any of the players' hole cards.) Interestingly, the cheater
folded the first two hands before this observer showed up, then did not fold a single hand before the flop for the next 20 minutes, and then folded his hand pre-flop when another player had a pair of kings as hole cards! This sort of cheating went on throughout the tournament.
So the poker detectives turned their attention to this observer. They traced the observer's IP address and account name to the same set of servers that host Absolute Poker, and also, apparently, to a particular individual named Scott Tom, who seems to be a part-owner of
Absolute Poker! If all of this is correct, it shows exactly how the cheating would have transpired: an insider at the Web site had real-time access to all of the hole cards (it is not hard to believe
that this capability would exist) and was relaying this information to an outside accomplice.
More details here.
http://forumserver.twoplustwo.com/showthreaded.php?Cat=0&Number=12523924&an=&page=0&vc=1
###
/// Quotes are from Griffith's translation of Sun Zi's AoW
Step 1: Know your target and know yourself
Therefore I say: 'Know the enemy and know yourself; in a hundred battles you will never be in peril. --- Chapter 3 – Offensive Strategy
Step 2: Decide to gather information
Now the reason the enlightened prince and the wise general conquer the enemy whenever they move and their achievements surpass those of ordinary men is foreknowledge. .... What is called 'foreknowledge' cannot be elicited from spirits, nor from gods, nor by analogy with past events, nor from calculations. It must be obtained from men who know the enemy situation. . .. And therefore only the enlightened sovereign and the worthy general who are able to use the most intelligent people as agents are- certain to achieve great things. Secret operations are essential in war; upon them the army relies to make its every move.
Step 3: Gather information on the target and the territory
Of all those in the army close to the commander none is more intimate than the secret agent; of all rewards none more liberal than those given to the secret agents; of all matters none more confidential than those relating to secret operations. -Chapter 13 Employment of Competitive Intelligence
Step 4: Determine the state of the territory.
In respect to the employment of troops, ground may be classified as dispersive, frontier, key, communicating, focal, serious, difficult, encircled, and death. ... Ground equally advantageous for the enemy or me to occupy is key ground. ... Do not attack an enemy who occupies key ground. ... In key ground I would hasten up my rear elements. - Chapter 11 Nine Grounds
Step 5: Plan and Decide.
"Now if the estimates made in the temple before hostilities indicate a victory it is because calculations show one's strength to be superior to that of his enemy; if they indicate defeat, it is because calculations show that one is inferior. With many calculations, one can win; with few one cannot. How much less chance of victory has one who makes none at all! By this means I examine the situation and the outcome will be clearly apparent.
Step 6: Lead by Prepositioning
Anciently the skillful warriors first made themselves invincible and awaited the enemy's moments of vulnerability. ... Invincibility depends on one's self; the enemy's vulnerability on him. ... It follows that those skilled in war can make themselves invincible but cannot cause an enemy to be certainly vulnerable. ... Therefore it is said that one may know how to win, but cannot necessarily do so. ... Invincibility lies in the defense; the possibility of victory in the attack. - Chapter 4 Disposition
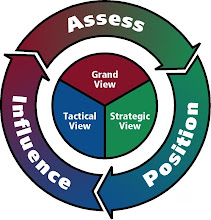
Building the Tangible Vision is Step 1-4.
Connecting with the Tangible Vision is Step 5
Leading with the Tangible Vision is Step 6.
###
I highly recommend the translations from Sawyer and Ames. Also recommend Mark McNeilly's book on applying Sun Zi's principles. It comes with Griffith's translation.

###
--- More to come ---


No comments:
Post a Comment