
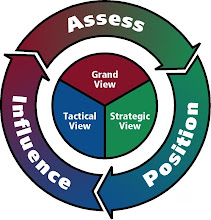
Before a game-changing move is implemented, the chief decision-maker(s) must decide whether the intended outcome is greater than the secondary after-effects. Conclusively, the decision-maker must also determine whether he or she is willing to live with the consequences from such disruption.
Whenever you are making a high level decision, can you see the impact of your decision? Can you see how strategically positioned you and your company will be, after the implementation of your decision?
Do you have a strategic process that allows you to see the strategic positioning outcome of your decision?
If not, contact us
#
By JOHN MARKOFF and THOM SHANKER
It would have been the most far-reaching case of computer sabotage in history. In 2003, the Pentagon and American intelligence agencies made plans for a cyberattack to freeze billions of dollars in the bank accounts of Saddam Hussein and cripple his government’s financial system before the United States invaded Iraq. He would have no money for war supplies. No money to pay troops.
“We knew we could pull it off — we had the tools,” said one senior official who worked at the Pentagon when the highly classified plan was developed.
But the attack never got the green light. Bush administration officials worried that the effects would not be limited to Iraq but would instead create worldwide financial havoc, spreading across the Middle East to Europe and perhaps to the United States.
Fears of such collateral damage are at the heart of the debate as the Obama administration and its Pentagon leadership struggle to develop rules and tactics for carrying out attacks in cyberspace.
While the Bush administration seriously studied computer-network attacks, the Obama administration is the first to elevate cybersecurity — both defending American computer networks and attacking those of adversaries — to the level of a White House director, whose appointment is expected in coming weeks.
But senior White House officials remain so concerned about the risks of unintended harm to civilians and damage to civilian infrastructure in an attack on computer networks that they decline any official comment on the topic. And senior Defense Department officials and military officers directly involved in planning for the Pentagon’s new “cybercommand” acknowledge that the risk of collateral damage is one of their chief concerns.
“We are deeply concerned about the second- and third-order effects of certain types of computer network operations, as well as about laws of war that require attacks be proportional to the threat,” said one senior officer.
This officer, who like others spoke on the condition of anonymity because of the classified nature of the work, also acknowledged that these concerns had restrained the military from carrying out a number of proposed missions. “In some ways, we are self-deterred today because we really haven’t answered that yet in the world of cyber,” the officer said.
In interviews over recent weeks, a number of current and retired White House officials, Pentagon civilians and military officers disclosed details of classified missions — some only considered and some put into action — that illustrate why this issue is so difficult.
Although the digital attack on Iraq’s financial system was not carried out, the American military and its partners in the intelligence agencies did receive approval to cripple Iraq’s military and government communications systems in the early hours of the war in 2003. And that attack did produce collateral damage.
Besides blowing up cellphone towers and communications grids, the offensive included electronic jamming and digital attacks against Iraq’s telephone networks. American officials also contacted international communications companies that provided satellite phone and cellphone coverage to Iraq to alert them to possible jamming and to ask their assistance in turning off certain channels.
Officials now acknowledge that the communications offensive temporarily disrupted telephone service in countries around Iraq that shared its cellphone and satellite telephone systems. That limited damage was deemed acceptable by the Bush administration.
Another such event took place in the late 1990s, according to a former military researcher. The American military attacked a Serbian telecommunications network and accidentally affected the Intelsat satellite communications system, whose service was hampered for several days.
These missions, which remain highly classified, are being scrutinized today as the Obama administration and the Pentagon move into new arenas of cyberoperations. Few details have been reported previously; mention of the proposal for a digital offensive against Iraq’s financial and banking systems appeared with little notice on Newsmax.com, a news Web site, in 2003.
The government concerns evoke those at the dawn of the nuclear era, when questions of military effectiveness, legality and morality were raised about radiation spreading to civilians far beyond any zone of combat.
“If you don’t know the consequences of a counterstrike against innocent third parties, it makes it very difficult to authorize one,” said James Lewis, a cyberwarfare specialist at the Center for Strategic and International Studies in Washington.
But some military strategists argue that these uncertainties have led to excess caution on the part of Pentagon planners.
“Policy makers are tremendously sensitive to collateral damage by virtual weapons, but not nearly sensitive enough to damage by kinetic” — conventional — “weapons,” said John Arquilla, an expert in military strategy at the Naval Postgraduate School in Monterey, Calif. “The cyberwarriors are held back by extremely restrictive rules of engagement.”
Despite analogies that have been drawn between biological weapons and cyberweapons, Mr. Arquilla argues that “cyberweapons are disruptive and not destructive.”
That view is challenged by some legal and technical experts.
“It’s virtually certain that there will be unintended consequences,” said Herbert Lin, a senior scientist at the National Research Council and author of a recent report on offensive cyberwarfare. “If you don’t know what a computer you attack is doing, you could do something bad.”
Mark Seiden, a Silicon Valley computer security specialist who was a co-author of the National Research Council report, said, “The chances are very high that you will inevitably hit civilian targets — the worst-case scenario is taking out a hospital which is sharing a network with some other agency.”
And while such attacks are unlikely to leave smoking craters, electronic attacks on communications networks and data centers could have broader, life-threatening consequences where power grids and critical infrastructure like water treatment plants are increasingly controlled by computer networks.
Over the centuries, rules governing combat have been drawn together in customary practice as well as official legal documents, like the Geneva Conventions and the United Nations Charter. These laws govern when it is legitimate to go to war, and set rules for how any conflict may be waged.
Two traditional military limits now are being applied to cyberwar: proportionality, which is a rule that, in layman’s terms, argues that if you slap me, I cannot blow up your house; and collateral damage, which requires militaries to limit civilian deaths and injuries.
“Cyberwar is problematic from the point of view of the laws of war,” said Jack L. Goldsmith, a professor at Harvard Law School. “The U.N. Charter basically says that a nation cannot use force against the territorial integrity or political independence of any other nation. But what kinds of cyberattacks count as force is a hard question, because force is not clearly defined.”
Copyright 2009 The New York Times Company
http://www.nytimes.com/2009/08/02/us/politics/02cyber.html

No comments:
Post a Comment